Windows 10 - Conclusion |
 The image on the left shows a group of geometric shapes in sequence, and new characters can be added if the image is enlarged. It illustrates the development and distribution service pattern of Windows 10. There is a check mark in the first box, which means that one of the original versions of the operating system is used. It is an association of different versions of the 'same' Windows 10 operating systems being upgraded sequentially. The computer is running 'Windows 10 PRO build 1607-x86' with 'NTLite' software and upgrade prevented. Knowing that in terms of compatibility with older software support there is no improvement at all using the x64 operating system, in fact a lot of software support does not work, is the reason for staying on the 'x86' system.
The image on the left shows a group of geometric shapes in sequence, and new characters can be added if the image is enlarged. It illustrates the development and distribution service pattern of Windows 10. There is a check mark in the first box, which means that one of the original versions of the operating system is used. It is an association of different versions of the 'same' Windows 10 operating systems being upgraded sequentially. The computer is running 'Windows 10 PRO build 1607-x86' with 'NTLite' software and upgrade prevented. Knowing that in terms of compatibility with older software support there is no improvement at all using the x64 operating system, in fact a lot of software support does not work, is the reason for staying on the 'x86' system.
Before replacing the GATEWAY (router) device, the entire realization of the home network shown in the following picture. Everything is 'bustling' with different cables. It's true that the new GATEWAY Fritz!Box has quite a few options, but his support for NAS is not a feature to be praised. But with its introduction into the system, the STB device (TV box) was also changed, which 'threw out' the WD TV Player device and its USB drive from the network. That is why the classic NAS should be replaced with a new one, which will have multimedia capabilities.

|
| Figure 4.6.72 Home network with multimedia accessories. |
Some computer components and peripherals were bought because their prices have dropped due to newer products, but they are sufficient for the previously described computer, and some were received as a gift, because they were outdated for the former owner, but they fit well into the home network shown. Not all previously listed components are shown in the picture of Home network, especially those connected to a PC. And the author's PC is not 'Alienware', but it would be nice if it was.
And in order for the PC to function properly and stably, it is not enough just to install the operating system. There is still a lot of work to get a nice colorful desktop with lots of icons, so when you click on one of them something happens.

|
| Figure 4.6.73 Colorful desktop of computers. |
This additional post-installation job is described below and the icons in the paragraphs guide the description of the use of each of these jobs. The jobs should be done in the order following the icons in the following paragraphs that describe each of these jobs to be done. Some jobs are done once, and some will need to be used continuously.
What kind of operating system is it if you have to constantly 'tinker' on it instead of using the installed useful software? Perhaps once in the future 'Windows 10' becomes a valid operating system. Who is waiting - welcome.
To begin with, above all the following, on the x86 32-bit OS, a one 'little thing' can be done to free up as much working memory as possible without intervention on kernel of OS:
 In order to achieve the stated goals, you should first use the software 'NTLite'. This perfection of software allows to remove everything possible from the installation media. It's amazing how many generic drivers, which basically serve no purpose, that Microsoft have 'inserted' into the installation media. Not only that, but they like to 'argue' with drivers that are better and installed by the user, but are not 'certified' by Microsoft. And there's everything from 'support' for various types of printers, modems, scanners, RAID drivers, loads of network card drivers and the like, all mostly for devices that no longer exist? Does it even have AGP port support? So why did they throw out the TWAIN protocol? All this is a legacy from the operating system 'Windows Vista RTM'. In addition, all kinds of software support regarding fonts and keyboards for different language areas are there, although the installation is basically done for one language area. In this sense, there are also unnecessary services. What will the author do with the news about Donald Trump, and that too in Croatia? He doesn't even need 'silly' mobile games? This is a DESKTOP computer for working at home! The most important thing is that with the processing of the installation ISO file, it will incorporate the latest cumulative update, and the necessary drivers for all built-in and external devices.
In order to achieve the stated goals, you should first use the software 'NTLite'. This perfection of software allows to remove everything possible from the installation media. It's amazing how many generic drivers, which basically serve no purpose, that Microsoft have 'inserted' into the installation media. Not only that, but they like to 'argue' with drivers that are better and installed by the user, but are not 'certified' by Microsoft. And there's everything from 'support' for various types of printers, modems, scanners, RAID drivers, loads of network card drivers and the like, all mostly for devices that no longer exist? Does it even have AGP port support? So why did they throw out the TWAIN protocol? All this is a legacy from the operating system 'Windows Vista RTM'. In addition, all kinds of software support regarding fonts and keyboards for different language areas are there, although the installation is basically done for one language area. In this sense, there are also unnecessary services. What will the author do with the news about Donald Trump, and that too in Croatia? He doesn't even need 'silly' mobile games? This is a DESKTOP computer for working at home! The most important thing is that with the processing of the installation ISO file, it will incorporate the latest cumulative update, and the necessary drivers for all built-in and external devices.
Since 'NTLite' deserves a special description, to which the small icon at the beginning of the previous paragraph leads, I will not talk about it anymore as a program support. I would just point out that the author of these lines used it a little unusually. The components were removed after all the contents from the installation media were installed on the computer and a complete 'update' was performed. Since the installed OS has the status R.I.P. components can be removed directly from the installed OS on disk without fear of some future cumulative upgrade bringing back a host of deleted or forced-in Microsoft magic. In addition, it can be quickly checked whether something unnecessary has been removed or not. Of course, everything should be written down in a comprehensible way so that the desired installation media could be created on the basis of it. I have to admit that I left the 'STORE' program support so that it could download geographical maps and some little things related to them.
 The drivers for the components built into the PC are of particular importance because they are interface between components and operating system. If you've lost your driver discs, you're unable to find drivers on the manufacturer's web site or Windows Update can't configure your hardware, use SDI tool to quickly find and install all missing drivers. If you're a PC technician, keep Snappy Driver Installer on your USB flash drive or external hard drive and take it with you wherever you go. In environments with no Internet access you can quickly start installing a drivers. No more searching for drivers after a clean install, just let Snappy Driver Installer do it's thing and your job will be done in no time. The development team of this software used considerable effort to make it efficient, portable and free.
The drivers for the components built into the PC are of particular importance because they are interface between components and operating system. If you've lost your driver discs, you're unable to find drivers on the manufacturer's web site or Windows Update can't configure your hardware, use SDI tool to quickly find and install all missing drivers. If you're a PC technician, keep Snappy Driver Installer on your USB flash drive or external hard drive and take it with you wherever you go. In environments with no Internet access you can quickly start installing a drivers. No more searching for drivers after a clean install, just let Snappy Driver Installer do it's thing and your job will be done in no time. The development team of this software used considerable effort to make it efficient, portable and free.
But that's not all when the operating system is installed. When everything is finally installed as Microsoft says, you still need:
 The Visual C++ Redistributable installs Microsoft C and C++ runtime libraries, part of MSVC - integrated development environment for the C and C++ programming languages. These libraries are required by many applications built using Microsoft C and C++ tools. The problem is that each new version of the newer program support has incompatible libraries with the previous ones, so this package contains versions from 2005, 2008, 2010, 2012, 2013 and 2022. If you were to search for these versions individually, you would find different subversions for each year, so it is better to take the package through this link because the author of package made an effort to somehow resolve all these disagreements. The package is called 'VisualCppRedist_AIO_x86_x64' and during installation it does not ask for any permissions for each annual sub-version and arranges all contents neatly. Of course, if it finds that it is a x32 operating system, it will not install the part related to the x64 operating system and vice versa.
The Visual C++ Redistributable installs Microsoft C and C++ runtime libraries, part of MSVC - integrated development environment for the C and C++ programming languages. These libraries are required by many applications built using Microsoft C and C++ tools. The problem is that each new version of the newer program support has incompatible libraries with the previous ones, so this package contains versions from 2005, 2008, 2010, 2012, 2013 and 2022. If you were to search for these versions individually, you would find different subversions for each year, so it is better to take the package through this link because the author of package made an effort to somehow resolve all these disagreements. The package is called 'VisualCppRedist_AIO_x86_x64' and during installation it does not ask for any permissions for each annual sub-version and arranges all contents neatly. Of course, if it finds that it is a x32 operating system, it will not install the part related to the x64 operating system and vice versa.
This is followed by the installation of the software '.Net Framework 4.8 Advanced Services', and if necessary, the older version '.Net Framework 3.5 must be is installed'.
There is another Microsoft product that needs to be installed. It is called 'Microsoft Edge WebView2 Runtime' and is regularly updated by Microsoft, and can be downloaded from the 'Microsoft Update Catalog' site. It is a good idea to install it, regardless of whether IE and Edge have been removed with 'NTlite', because it is used by the some manufacturers for the operation of their software.
 Microsoft DirectX is a group of technologies designed to make Windows-based computers an ideal platform for running and displaying applications rich in multimedia elements such as full-color graphics, video, 3D animation, and rich audio. The app includes security and performance updates, along with many new features across all technologies, which can be accessed by applications using the DirectX APIs, The most recent version of this software is an integral part of the OS installation, but it does not support the older software.
Microsoft DirectX is a group of technologies designed to make Windows-based computers an ideal platform for running and displaying applications rich in multimedia elements such as full-color graphics, video, 3D animation, and rich audio. The app includes security and performance updates, along with many new features across all technologies, which can be accessed by applications using the DirectX APIs, The most recent version of this software is an integral part of the OS installation, but it does not support the older software.
Therefore, according to the author's recommendation, you should first install an older version of DirectX, for example, version DirectX_9c-2006 (May - June 2006), size 52.32 MB, which supports software from the era of Windows 95 / Windows 98 / Windows 2000 / Windows XP / Windows Vista / Windows Vista x64 / Windows XP x64 / Windows ME / Windows NT 4.0 / Windows 7 / Windows 7 x64 / Windows 8 / Windows Server 2003 x64 / Windows Server 2003 / Windows Server 2008 / Windows 8 x64 / Windows NT / Windows 2000 x64. Then install newer version of DirectX_9c-2011 (March - June 2010), size 95.6 MB, which updates the previous version and supports software for Windows 98 / Windows 2000 / Windows XP / Windows Vista / Windows 7. The most recent version is integrated into the operating system that is being installed.
Older versions do not affect the version of DirectX installed, but installs a number of optional parallel technologies from the legacy DirectX SDK (Software Development Kit) used by some older games, contains a set of tools for 'third-party' developers.
Features of DirectX technologies are:
 There is still 12 GB of 'invisible' memory left for the x86 system, which should be used somehow. For this purpose, the software 'Primo Ramdisk Professional Edition v6.6.0' was used. The icon at the beginning of the paragraph is a link to their pages. This product is already described for the 'Windows XP' operating system version. During purchase, installation and activation, it must be activated via a 'key' obtained from the manufacturer, so that this program support is activated as a 'BOOT' service and is immediately available to the operating system. The instructions at their site are very helpful and worth reading. When the operating system is active, the 'Romex' software can be accessed. First, access to the 'invisible' memory is activated, then the RAMDISK is created, and finally the directories in it where temporary data will be placed.
There is still 12 GB of 'invisible' memory left for the x86 system, which should be used somehow. For this purpose, the software 'Primo Ramdisk Professional Edition v6.6.0' was used. The icon at the beginning of the paragraph is a link to their pages. This product is already described for the 'Windows XP' operating system version. During purchase, installation and activation, it must be activated via a 'key' obtained from the manufacturer, so that this program support is activated as a 'BOOT' service and is immediately available to the operating system. The instructions at their site are very helpful and worth reading. When the operating system is active, the 'Romex' software can be accessed. First, access to the 'invisible' memory is activated, then the RAMDISK is created, and finally the directories in it where temporary data will be placed.
It is important to emphasize that in order for RAMDISK software to behave correctly in accordance with the OS, the environment variables in the 'System' menu need to be set correctly, as shown in the following Figure.
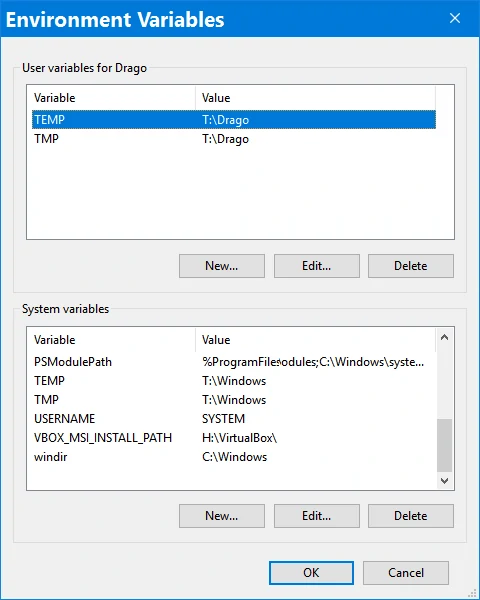
| |
| Figure 4.6.74 Environment Variables. |
 In order for the system partition not to be filled with data and results of software working, it is necessary to move the working directories. What the operating system allows is shown in the picture 4.6.28, what the software allows is shown in image 4.6.32, while for the rest the software support 'Link Shell Extension (LSE)'. Regardless of the above, the author uses LSE for all redirects because that approach has been shown to be more secure. It is impossible to briefly describe what can be done by redirecting individual directories of the operating system, especially the part for the user, so that the OS always remains almost 'clean' during operation. The icon at the beginning of the paragraph is a link to the LSE site. x86 and x64 version of this software can be downloaded here.
In order for the system partition not to be filled with data and results of software working, it is necessary to move the working directories. What the operating system allows is shown in the picture 4.6.28, what the software allows is shown in image 4.6.32, while for the rest the software support 'Link Shell Extension (LSE)'. Regardless of the above, the author uses LSE for all redirects because that approach has been shown to be more secure. It is impossible to briefly describe what can be done by redirecting individual directories of the operating system, especially the part for the user, so that the OS always remains almost 'clean' during operation. The icon at the beginning of the paragraph is a link to the LSE site. x86 and x64 version of this software can be downloaded here.
Shield icons indicate that software is running in some 'compatibility' mode (Figure 4.6.74). The organization of the disk system and the installation of the operating system and software resulted in the concept of data organization according to the following Figure with the use of many links made with the software 'Link Shell Extension' (LSE), which you can download here.
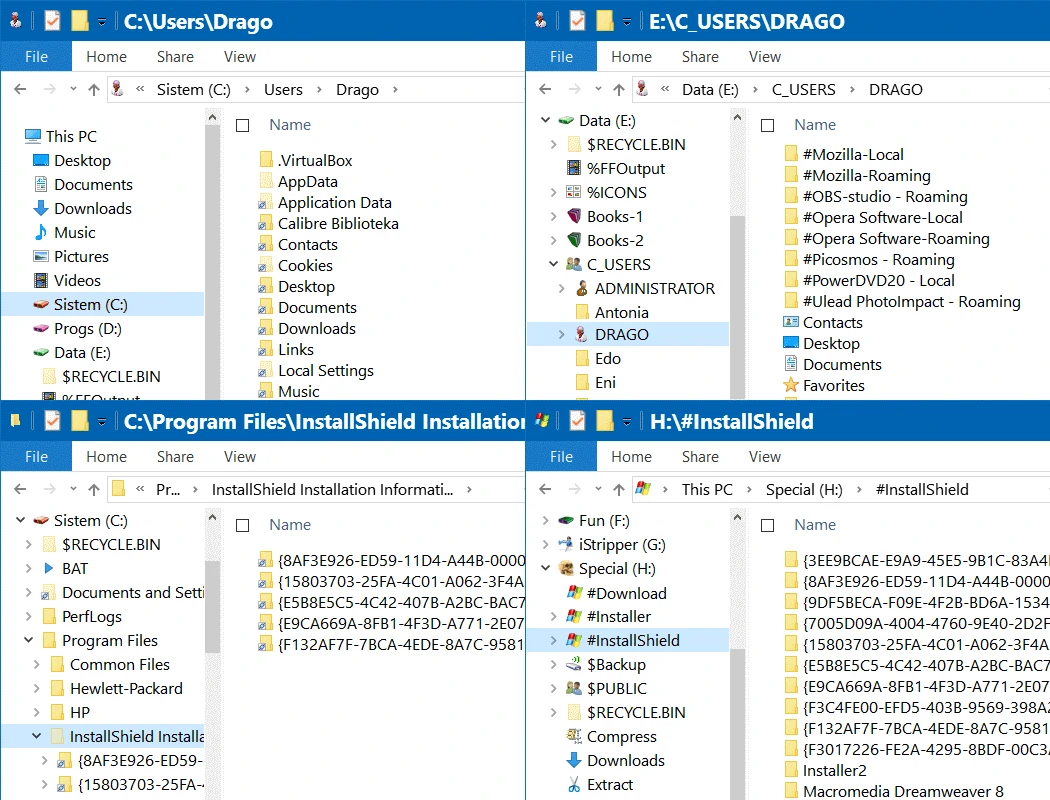
|
| Figure 4.6.75 Moving folders (directories) using LSE. |
The previous Figure shows four interesting clips of File Explorer (FE), or as it is also called Windows Explorer (WE). The first one above, on the left, shows the links of the user on the [C:] disk partition, created with the LSE software, which all the user folders of the user DRAGO are redirected to the directory [E:\C_USERS\DRAGO], as shown in the screenshot to the right of the above. There are [#....] directories which are nothing but working files of the used software. In this way, all dynamic content has been relocated. In the lower, left clip, the images are shown with LSE relocated folders of directory [C:\Program Files\InstallShield Installation] to directory [H:/#INSTALLER] shown in the clip on the right, below. Since the number of files in the prelaced location is larger, it is clear that other installation files are also directed to that location. In this way, the [C:] partition is freed from multiple writes and is therefore fast, of course with the added help of 'RamDisk' on the [P:] partition. For LSE software, the rule applies that the link should have the same name as the name of the directory it replaces, and you can specify another place with a different destination name in the link.
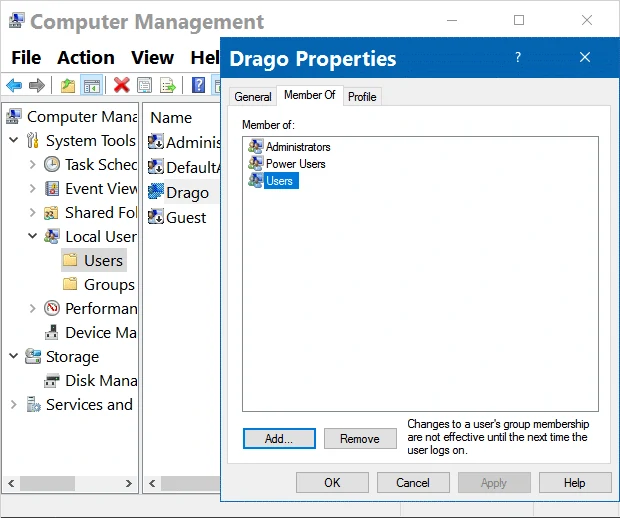
The following Higures shows how a file (or partition or directory), or some other object, is assigned which users have the right to access it.
|

|
|
| Figure 4.6.76 User Peroperties, group membership. | Figure 4.6.77 File Properties. |
First, the rights of the user DRAGO were extended with membership to the groups 'Power Users' and 'Users'. The 'Users' group is more important because it includes all users defined on the computer. Then each partition was given the recursive right to be used by a user from the group 'Users', so the file '#_Tina.bmp', as well as the directory where it is located. As, for example, the directory [C:\ProgramData] is under the authority of the system, if you want to access it easily, you should add the user 'Users' as the next set of images describes.
 |
| Figure 4.6.78 Object Permissions. ( + / - ) |
Now the user 'Users' can freely 'walk' through the [C:\ProgramData] directory, but the owner is still 'System', and if you want the user to be able to change something, you should give him the auditing rights as shows the next set of images, without displaying the middle selection as into the previous set of images.
 |
| Figure 4.6.79 0bject Auditing. ( + / - ) |
As the NTFS file system stores information about partitions, directories and files in the headers of individual objects, it can easily happen that when copying some contents of someone else's USB disk, some parameters in the contents of someone else's USB disk cannot be changed USB drive, or no data access rights at all. A similar thing can happen during the installation of some program support that will install one of its 'unknown trusted user'. Then the described tools come to the rescue. In summary, 'Auditing' (Figure 4.6.78) is used to add rights to an object for a selected user of some group (eg USERS, Figure 4.6.75) so that he can only read contents or more advanced rights but without changing ownership of the object, 'Permissions' (Figure 4.6.77) serves to change the ownership of an object, with the fact that the selected user must already be defined with 'Auditing', and finally the selected user is added to the 'Properties' list (Figure 4.6.76) in order to apply the first two settings. Just adding the user to the 'Properties' list has no effect, because you cannot set his authority over the object in that window if 'Auditing' is not set for him.
Activating the sowtware [C:\Windows\System32\ gpedit.msc] activates the service for editing many operating system parameters, the 'group policy management console' for configuring different group policies. The following is a picture of the initial window and an example of use, which is related to the prohibition of the installation of drivers by the OS. Namely, the Windows OS uses some generic (general) drivers with which it knows how to override slightly older drivers that are more complete and work better during the update process.
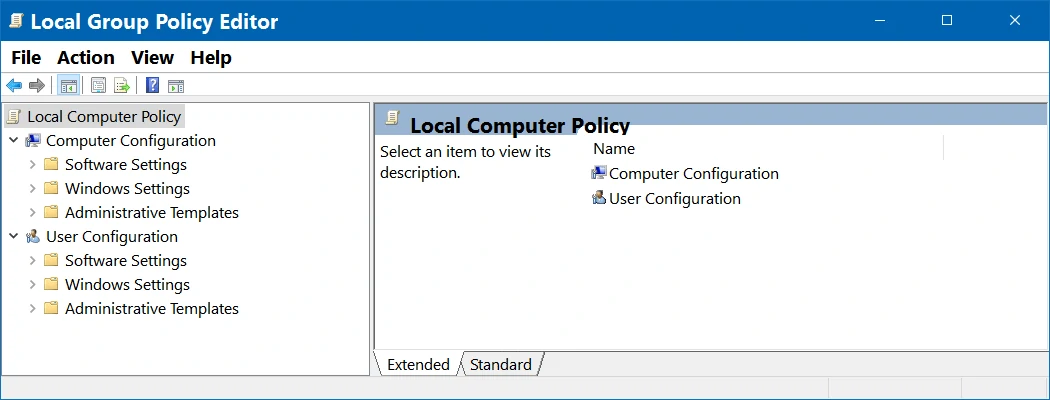 |
| Figure 4.6.80 Local Gropup Policy. ( + / - ) |
This service is not available by default in the 'HOME' version of the OS, but it can be upgraded. Using it, on the server version of the OS everything is forbidden by default, while in other versions of the OS everything is undefined by default.
Activating software [C:\Windows\System32\ secpol.msc] activates a service similar to the previous one, 'Local Security Policy Manager' which is used to manage and administer different security parameters of the computer operating system. The following is a picture of the initial window and an example of use.
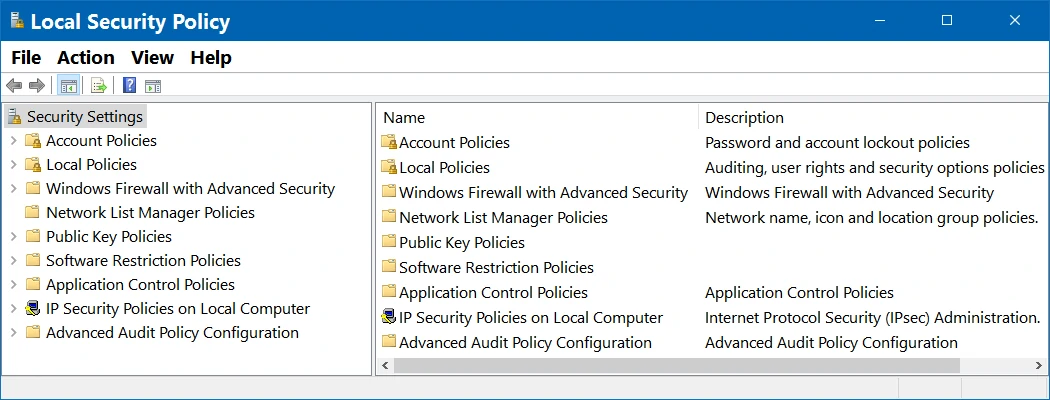 |
| Figure 4.6.81 Local Security Policy. ( + / - ) |
So, mostly something is prohibited there, and in this example, the prohibition of executing the UPGRADE program and the prohibition of registering the Web-Camera program, which is not updated anyway, and there is no one to register because that service is no longer available.
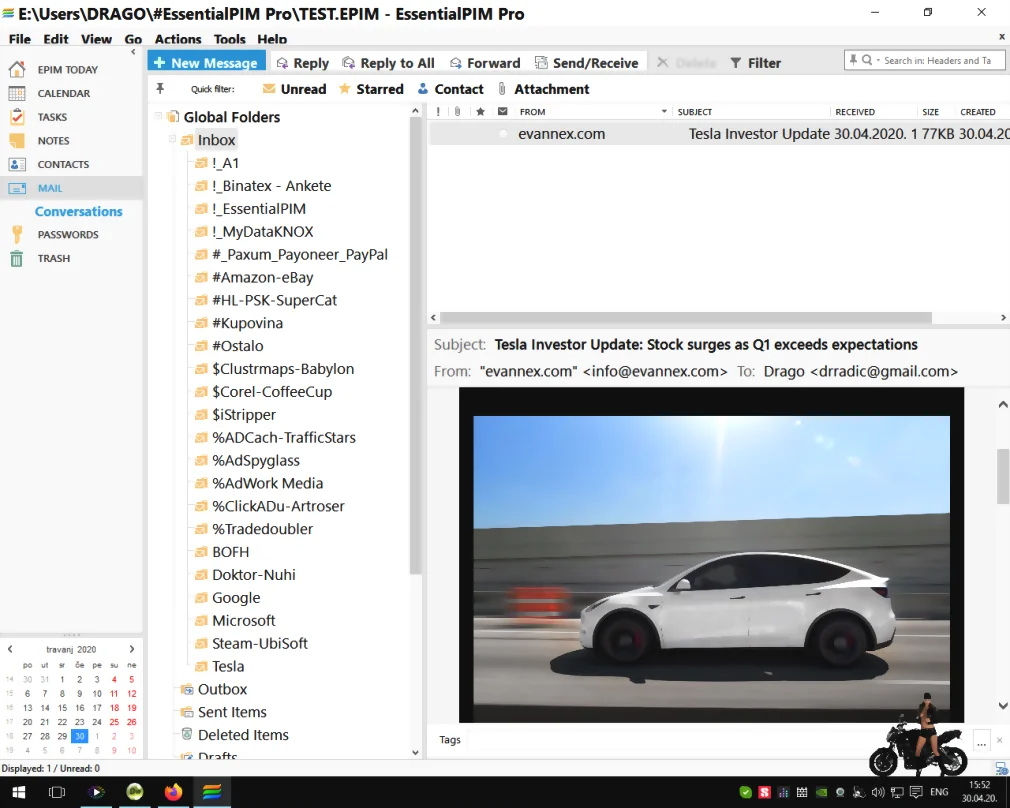
 All other activities regarding upgrades of OS are without significance. Since the entire 'Microsoft Office' suite is not installed, some components are blocked for upgrading because not present at all. No worries, the installed parts of this package will be upgraded, as well as the updates and definitions of the anti-virus program (Windows Defender), and occasionally some critical patches. The 'EssentialPim' software is used for email, as Microsoft software have been shown to be 'vulnerable' for the same purpose. Its use is not a commercial for them, but a solution found by the author who has the most commonly solved 'INBOX' for all user accounts, and is not 'vulnerable'. There is a free and PRO version that is payable one time. A useful feature of this e-mail client is support for PGP.
All other activities regarding upgrades of OS are without significance. Since the entire 'Microsoft Office' suite is not installed, some components are blocked for upgrading because not present at all. No worries, the installed parts of this package will be upgraded, as well as the updates and definitions of the anti-virus program (Windows Defender), and occasionally some critical patches. The 'EssentialPim' software is used for email, as Microsoft software have been shown to be 'vulnerable' for the same purpose. Its use is not a commercial for them, but a solution found by the author who has the most commonly solved 'INBOX' for all user accounts, and is not 'vulnerable'. There is a free and PRO version that is payable one time. A useful feature of this e-mail client is support for PGP.
|
| Figure 4.6.82 Client for e-mail / PAE. ( + / - ) |
When everything is finally installed, upgraded and adjusted, make a backup, and use the next tool to make the final adjustments and cleanings, and then finally 'patch' the operating system core (kernel).
 CCleaner is the number-one tool for cleaning PC. It protects your privacy and makes your computer faster and more secure! Takes care of Driver Update, PC Health, Cleaning registry and temporarily files, takes care about services, helps about PC boot time and performances and have much more other Tools to keep PC fast and efficiant. Author of this page uses aditional tools, like 'DISM++' (a utility for advanced users to clean, slim, backup, update, or recover your Windows operating system), 'PatchCleaner' (cleaning an orphaned installation files and is tagged to be moved or deleted), 'TweakNow Powerpack' (A complete pack of system optimization tools), 'Winaero Tweaker' (setting various settings) and 'WiseRegCleaner'. After using these tools, you must use 'wushowhide.diagcab' to check if automatically UPGRADE remained. It can happen that these tools violate some license or something else, and some parts of the registry should be kept in reserve (like exported .reg files). You can download these little tools here. It will work without installation regardless of which directory they are copied to.
CCleaner is the number-one tool for cleaning PC. It protects your privacy and makes your computer faster and more secure! Takes care of Driver Update, PC Health, Cleaning registry and temporarily files, takes care about services, helps about PC boot time and performances and have much more other Tools to keep PC fast and efficiant. Author of this page uses aditional tools, like 'DISM++' (a utility for advanced users to clean, slim, backup, update, or recover your Windows operating system), 'PatchCleaner' (cleaning an orphaned installation files and is tagged to be moved or deleted), 'TweakNow Powerpack' (A complete pack of system optimization tools), 'Winaero Tweaker' (setting various settings) and 'WiseRegCleaner'. After using these tools, you must use 'wushowhide.diagcab' to check if automatically UPGRADE remained. It can happen that these tools violate some license or something else, and some parts of the registry should be kept in reserve (like exported .reg files). You can download these little tools here. It will work without installation regardless of which directory they are copied to.
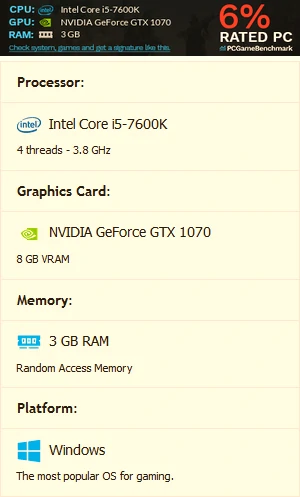
 32-bit operating systems have a limit on the amount of addresses available for RAM and various other components. Depending on your setup, this can limit the amount of RAM your system can support to somewhere around 3 GB - although it could be slightly higher or slightly lower. A technique called 'Physical Address Extension', or PAE, can allow a 32-bit OS to support up to 64 GB of RAM. By increasing the physical address size from 32 bits to 36 bits, there are plenty more addresses available for the system to use. Unlock up to 64 GB of RAM on 32-bit Windows with PAE Patch written by Brad Jones for patching OS kernel. Warning! Do not use patched kernel for eg. Cumulative Update for Windows. Use standard kernel and if needed patch kernel again. Since the x32 operating system is no longer supported, as a user I don't care. I'm not looking for new software, firmwares, drivers or patches, just a daily antivirus update.
32-bit operating systems have a limit on the amount of addresses available for RAM and various other components. Depending on your setup, this can limit the amount of RAM your system can support to somewhere around 3 GB - although it could be slightly higher or slightly lower. A technique called 'Physical Address Extension', or PAE, can allow a 32-bit OS to support up to 64 GB of RAM. By increasing the physical address size from 32 bits to 36 bits, there are plenty more addresses available for the system to use. Unlock up to 64 GB of RAM on 32-bit Windows with PAE Patch written by Brad Jones for patching OS kernel. Warning! Do not use patched kernel for eg. Cumulative Update for Windows. Use standard kernel and if needed patch kernel again. Since the x32 operating system is no longer supported, as a user I don't care. I'm not looking for new software, firmwares, drivers or patches, just a daily antivirus update.
Here is how PAE affects computer performance with the help of newer software testing support:
|

|

|
| Figure 4.6.83 Testing the PAE effect. | ||
There is more, but who will remember everything. True, the author has his own 'to-do' list for cleaning windows with 'NTLite' and installing 'Windows 10 PRO 1607 - x86 / version 10.0.14393.2214'. Maybe publish them sometime. Regarding the above image, if the processor 'Core i7-7700K' is used, the score is 75%.
Of course, after everything done according to the description in the above two paragraphs, you should make a backup again. According to the organization of the described computer, the [C:] and [D:] partitions are backed up with 'GHOST' software installed at USB stick, and as the other partitions contain mostly data and games, copy it all to an external USB drive or NAS.
 There is a better solution than the described. On the pages of 'SoftComputers © Digital product keys' site, an online store of digital goods which sell original activation codes and keys for software and operating systems, you can buy a license for 'Windows 10 Enterprise LTSB 2016', 'Windows 10 Enterprise LTSC 2019' or 'Windows 10 Enterprise LTSC 2021' for a very reasonable price, and download the .ISO file. These versions do not have a bunch of advertising content like 'Home' and 'Pro' versions. Therefore there is not much to 'clean', and they are related to server solutions by age at name of OS. 'Windows 10 Enterprise LTSB 2016' is a special version of Windows 10, created with more robust fault tolerance. A very good solution for older computers. Especially since the update contains '.Net Framework 3.5 (includes .Net 2.0 and 3.0)', '.Net Framework 4.6 Advanced Services', 'Internet Explorer 11' (its 'engine' is important), and 'Microsoft Edge' (contains new Chrome 'engine' - blink); software important for the operation of older versions of work programs and games. If necessary, it can always be downloaded and installed later '.Net Framework 4.8' (with in-place update to versions 4, 4.5, 4.5.1, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1 and 4.7.2.).
There is a better solution than the described. On the pages of 'SoftComputers © Digital product keys' site, an online store of digital goods which sell original activation codes and keys for software and operating systems, you can buy a license for 'Windows 10 Enterprise LTSB 2016', 'Windows 10 Enterprise LTSC 2019' or 'Windows 10 Enterprise LTSC 2021' for a very reasonable price, and download the .ISO file. These versions do not have a bunch of advertising content like 'Home' and 'Pro' versions. Therefore there is not much to 'clean', and they are related to server solutions by age at name of OS. 'Windows 10 Enterprise LTSB 2016' is a special version of Windows 10, created with more robust fault tolerance. A very good solution for older computers. Especially since the update contains '.Net Framework 3.5 (includes .Net 2.0 and 3.0)', '.Net Framework 4.6 Advanced Services', 'Internet Explorer 11' (its 'engine' is important), and 'Microsoft Edge' (contains new Chrome 'engine' - blink); software important for the operation of older versions of work programs and games. If necessary, it can always be downloaded and installed later '.Net Framework 4.8' (with in-place update to versions 4, 4.5, 4.5.1, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7, 4.7.1 and 4.7.2.).
The author of these lines bought an 'x86' OS license from them and got a discount for the 'x64' version. The installation process is similar for both systems, but if someone decides to buy the mentioned products, they can expect quite a bit of hassle to upgrade the OS to the latest release. Therefore, I do not recommend it to less skilled users, who are not very familiar with the OS. Installing the latest update provides completely updated OS files as well as generic drivers, and the author of these pages can safely say that he has never used a better and more stable OS of many of these products. But he suffered well to upgrade the OS to the latest working version 'Windows 1607 build 14393.6252' (September, 12. 2023).
SUMMARY:
 All the above tests were performed on a computer with the operating system 'Windows 10 v1607-x86 build 14393.2214'. Why x86 type OS? That's because a lot of 'older' programs are used that don't work on the x64 platform. More precisely, all software of the author is of x86 type, so he does not need an x64 solution. The x86 version is smaller and therefore loads faster, while the newer x64 versions require even better resources and are almost unusable without the use of SSD disks. Using the 'M.2 SSD 2280' module gives very good results in terms of OS speed. The operating speed of the OS and program support is much more acceptable, and working on the computer itself is more pleasant. Even better results would be achieved with a newer generation of this type of motherboard, as shown in Figure 3.5.48. M.2 slots support 'M.2 SATA SSD' or 'M.2 PCIe SSD' and support RAID configuration. In addition, the development of these modules is progressing daily, so that there are already versions that support the PCIe 5.0 bus. But the popular proverb always applies: 'How much money - so much music'.
All the above tests were performed on a computer with the operating system 'Windows 10 v1607-x86 build 14393.2214'. Why x86 type OS? That's because a lot of 'older' programs are used that don't work on the x64 platform. More precisely, all software of the author is of x86 type, so he does not need an x64 solution. The x86 version is smaller and therefore loads faster, while the newer x64 versions require even better resources and are almost unusable without the use of SSD disks. Using the 'M.2 SSD 2280' module gives very good results in terms of OS speed. The operating speed of the OS and program support is much more acceptable, and working on the computer itself is more pleasant. Even better results would be achieved with a newer generation of this type of motherboard, as shown in Figure 3.5.48. M.2 slots support 'M.2 SATA SSD' or 'M.2 PCIe SSD' and support RAID configuration. In addition, the development of these modules is progressing daily, so that there are already versions that support the PCIe 5.0 bus. But the popular proverb always applies: 'How much money - so much music'.
The described OS version is no longer updated, except for anti-virus software support, necessary security flaws and the like. In addition, Microsoft's failures must be endured, and as the working interface is increasingly adapted to mobile devices (desktop and mobile), it is quite ugly on a desktop computer. There are several reasons for using an older x32 version of Windows OS:
Microsoft has announced that it will soon discontinue support for x86 software support in its entirety. Furthermore, in addition to functioning as a service, using software in the 'cloud', software vendors are behaving similarly, which is increasingly becoming a service. It turns out that it is more efficient to use a fast Internet connection than to rely on slower disks. So, everything goes for rent.
|
Citing of this page: Radic, Drago. " Informatics Alphabet " Split-Croatia. {Date of access}; https://informatics.buzdo.com/file. Copyright © by Drago Radic. All rights reserved. | Disclaimer |